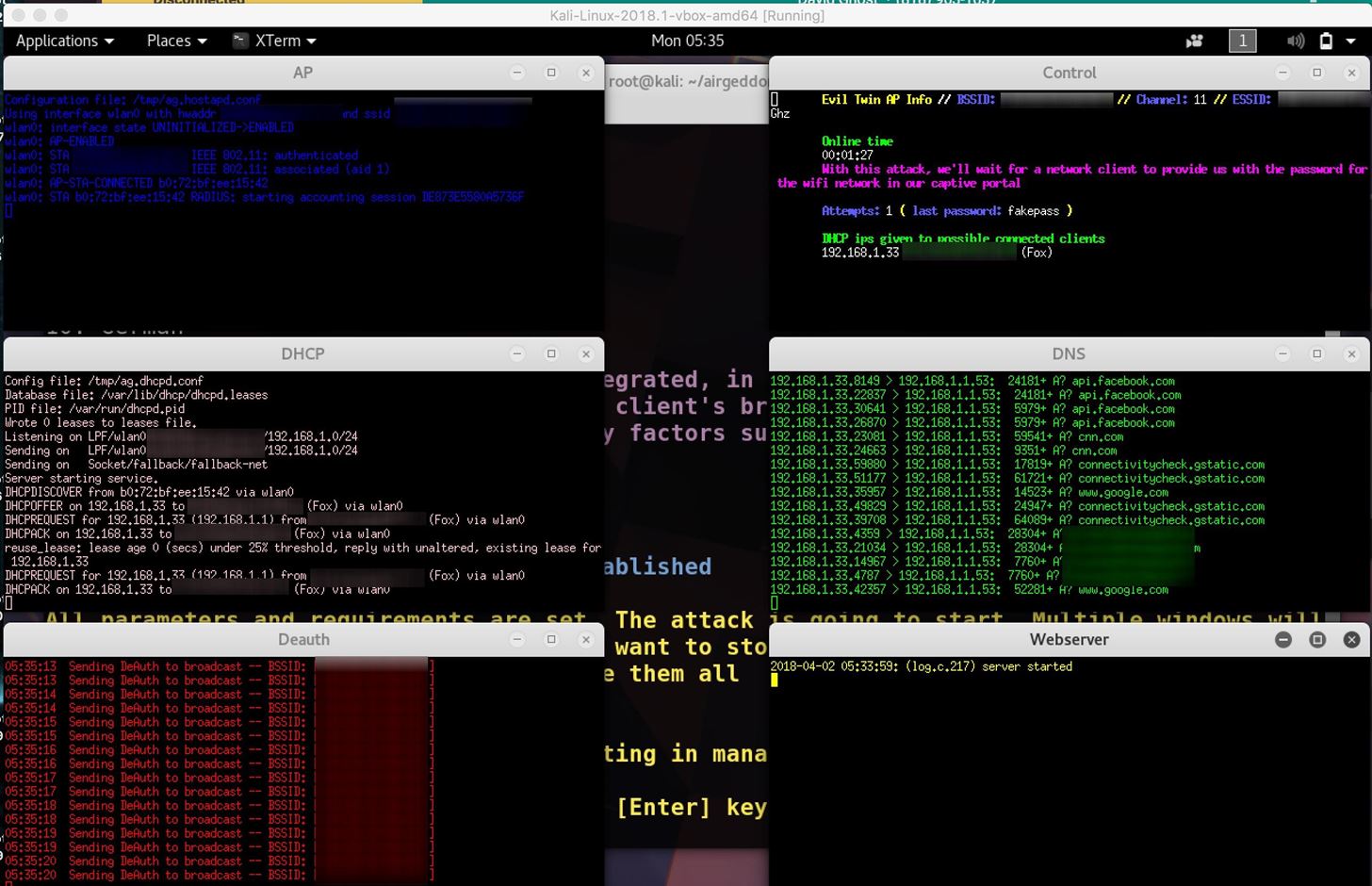
Ethical Hacking wifi hacking | Evil-Twin Attack Part 18 of Ethical Hacking??? #ethicalpakistan #hackingpakistan #blackhathacking #ethicalacademy #Eviltwinattack #fluxion... | By Ethical And Black Hat Academy | Facebook

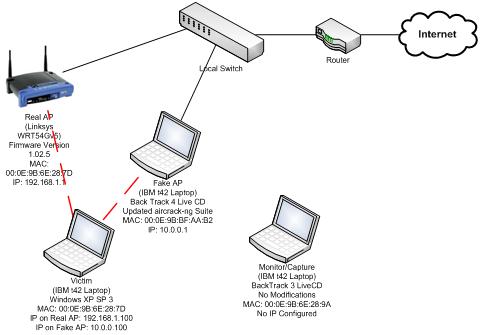
How to Hack Wi-Fi: Creating an Evil Twin Wireless Access Point to Eavesdrop on Data « Null Byte :: WonderHowTo

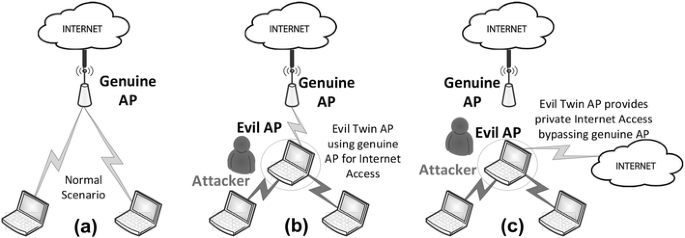
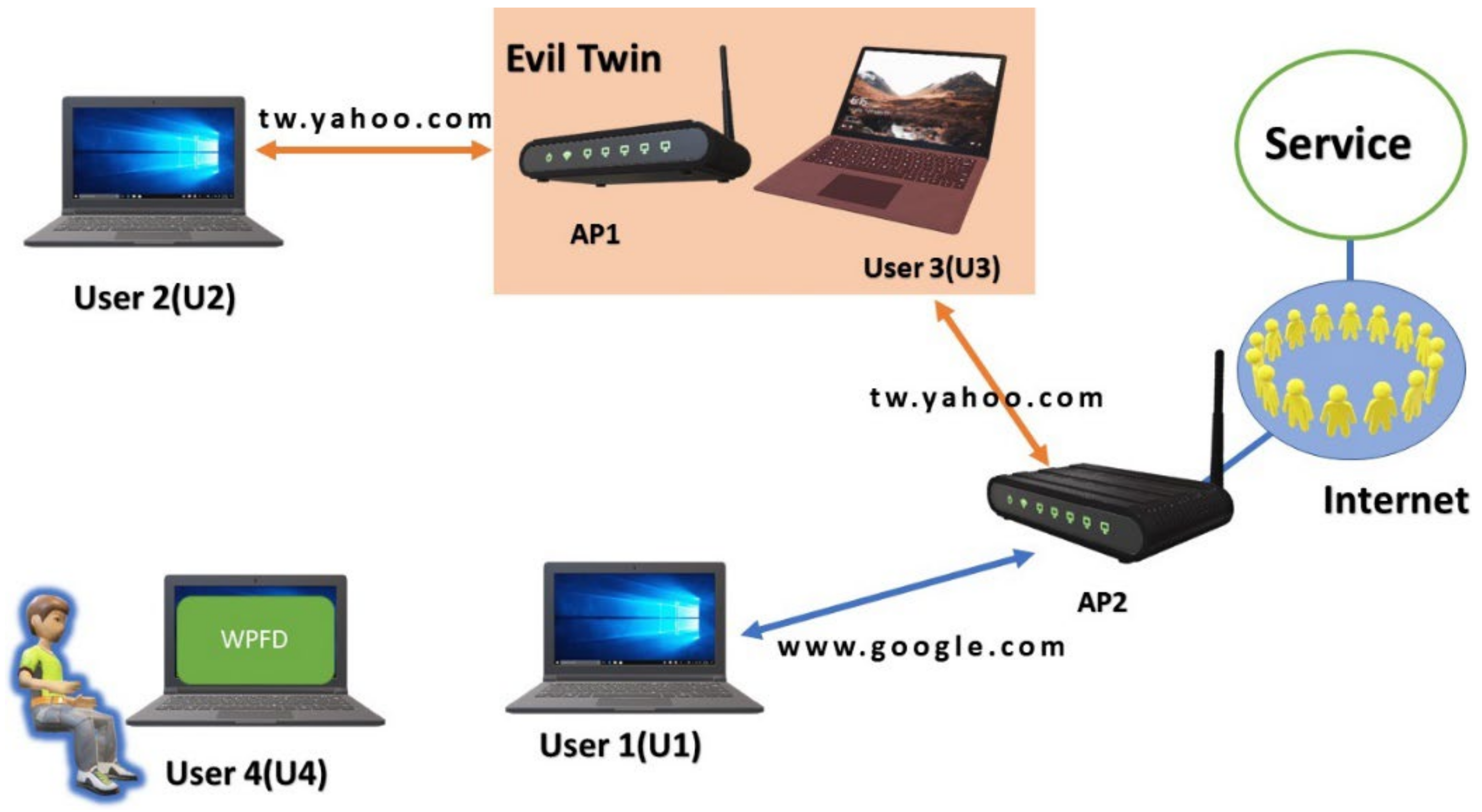
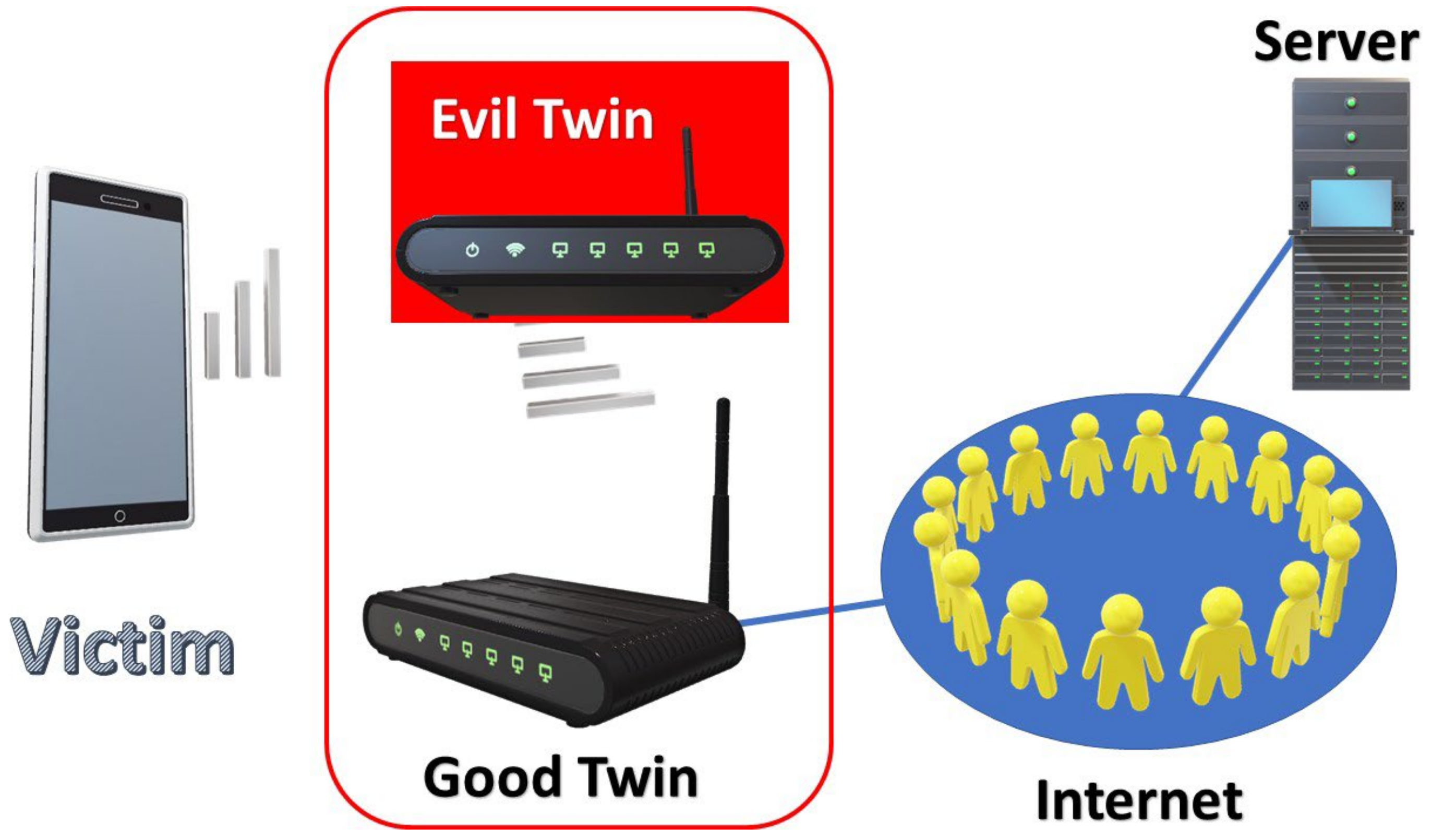
A passive user‐side solution for evil twin access point detection at public hotspots - Hsu - 2020 - International Journal of Communication Systems - Wiley Online Library

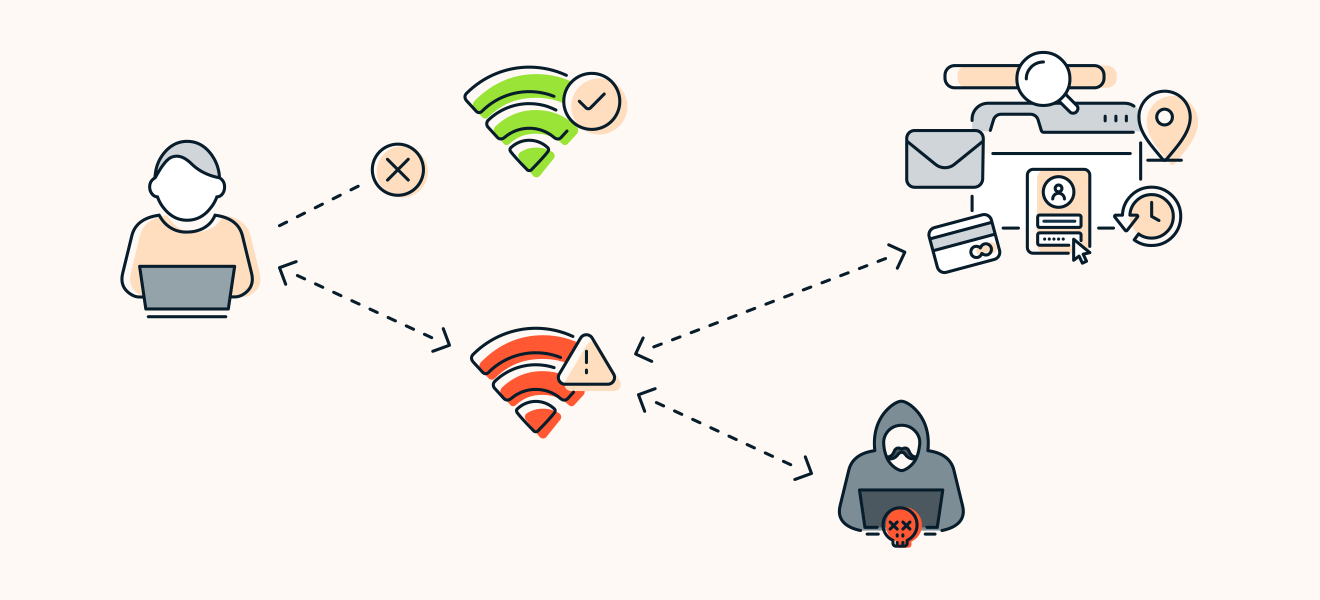
Don't fall victim to an evil twin attack. Here's how you can protect yourself - My Siccura - Private and Secure Digital Life